Security & Privacy
electobox uses state-of-the-art cryptographic algorithms and security systems to ensure vote privacy, election integrity, and voting transparency.
Core Security Principles
Every aspect of electobox is engineered around four foundational security guarantees.
Vote Privacy
No one — not even electobox — can read the contents of a vote. Votes are encrypted end-to-end and never decrypted individually.
Election Integrity
Mathematical proofs guarantee the correct execution of every step — from vote casting to tallying results.
Transparency
All processes produce verifiable cryptographic proofs that anyone can independently audit and verify.
Distributed Trust
No single entity holds the complete decryption key. Multiple trustees must collaborate to decrypt the tally.
End-to-End Encryption
Each vote is encrypted on the voter's device before being sent to the digital ballot box. Using strong cryptographic algorithms — similar to those used in e-banking — the vote remains unreadable throughout the entire process.
Even if an attacker intercepted a vote in transit, they could not decode its contents. The encryption happens entirely in the voter's browser, meaning the vote is never transmitted in plaintext.
Validity Check of the Vote
When a vote is cast, electobox validates it using a set of mathematical proofs generated during encryption — without ever decrypting it. This ensures no invalid or corrupted votes enter the ballot box while maintaining absolute secrecy.
Format Validation
The encrypted vote's mathematical structure is verified to confirm it conforms to the expected ballot format.
Proof Verification
Zero-knowledge proofs attached to each vote are checked to ensure correctness without revealing contents.
Secrecy Preserved
The entire validation process operates on encrypted data — the vote is never decrypted during verification.
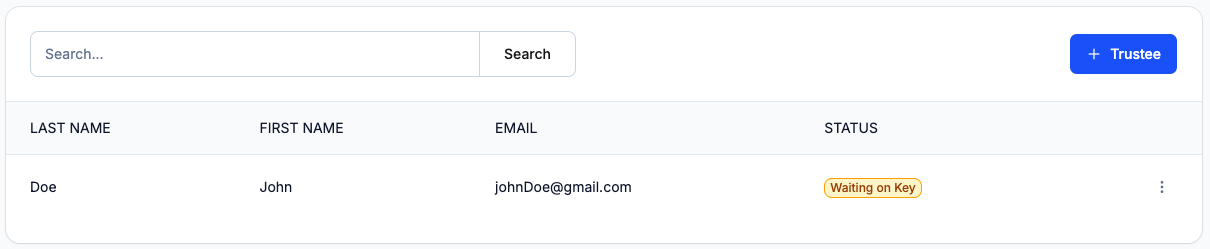
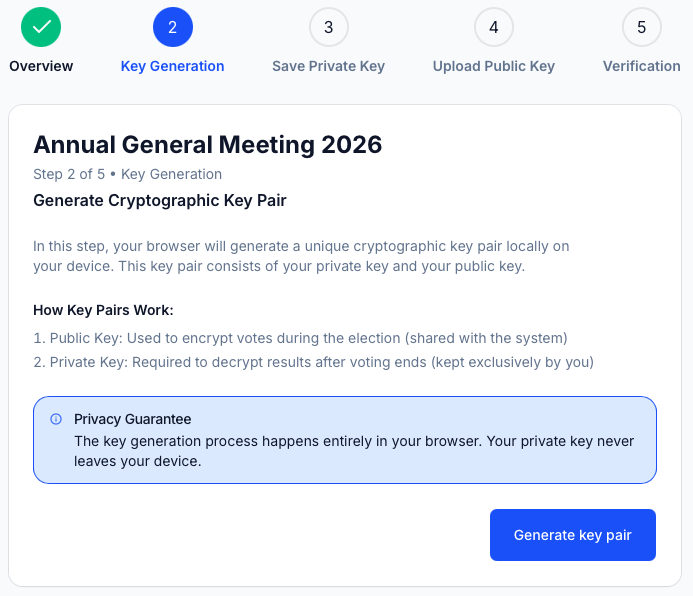
Only Your Selected Committee Has Access
Votes are encrypted using multiple cryptographic keys, each held by a different member of the electoral committee (trustee). Decryption requires the collaboration of all trustees.
No single person — not even electobox — can decrypt votes alone. This is called threshold encryption, and it ensures that trust is distributed across multiple independent parties.
Each trustee holds a unique partial key
No single key can decrypt votes
All trustees must collaborate for decryption
Mathematically Proven Cryptography
All election stages produce mathematical proofs (zero-knowledge proofs) that verify correct execution. These proofs can be verified by anyone without revealing voter identities or vote contents.
Vote Encryption Proofs
Proves the vote was correctly encrypted and conforms to the expected ballot structure.
Mixing Proofs
Proves votes were correctly anonymized through the cryptographic mixing process.
Decryption Proofs
Proves that each trustee's partial decryption was performed correctly and honestly.
Tallying Proofs
Proves the final count matches the decrypted votes with mathematical certainty.
Backup & Restore
Complete data backup and recovery capabilities ensure that no votes are lost, even in the event of system disruptions. The cryptographic integrity of the ballot box is maintained at all times.
Continuous Backups
Every vote and audit record is continuously backed up with redundant storage across multiple availability zones.
Instant Recovery
In the event of a disruption, the system can be restored to the exact state ensuring zero vote loss.
Integrity Verification
Cryptographic hashes ensure that restored data is bit-for-bit identical to the original ballot box.
Vote Anonymization
Verifiable Mixnet
After voting closes, electobox performs a cryptographic mixing process that breaks all links between encrypted votes and voters. This re-encrypts and shuffles every vote, making it mathematically impossible to trace a vote back to its caster.
The process produces mathematical proof that the mixing was done correctly — anyone can verify that votes were properly anonymized without knowing which vote belongs to which voter.
Verifiable shuffle: The mixing proof guarantees that the set of votes after mixing is exactly the same set of votes before mixing — just in a different, unlinkable order.
How the Mixnet Works
Collect Encrypted Votes
All encrypted votes are gathered from the ballot box.
Re-encrypt & Shuffle
Votes are re-encrypted and randomly shuffled, breaking all voter–vote links.
Generate Mixing Proof
A mathematical proof is produced to certify the shuffle was correct.
Public Verification
Anyone can verify the proof to confirm anonymization integrity.
Vote Receipt
Digitally signed by electobox
Your vote has been successfully recorded
Receipt Tracking Code
a3f8...c29d
Verifiable after election ends
Signature: 0x7a8b...4e2f
Timestamp: 2026-04-28T14:30:00Z
Digitally Signed Vote Receipts
After casting a vote, voters receive a digitally signed receipt proving their vote was successfully recorded. This receipt contains a unique tracking code linked to the encrypted vote.
After the election ends, voters can verify their vote is included in the final tally using this receipt — without revealing what they voted for. This provides individual verifiability while maintaining complete ballot secrecy.
Proves your vote was recorded in the ballot box
Verify inclusion in final tally after election ends
Never reveals your vote choice to anyone
Data Security & Compliance
Enterprise-grade infrastructure and regulatory compliance you can rely on.
EU Data Storage
All data is stored in European Union data centers, ensuring compliance with EU data residency requirements.
GDPR Compliant
Full compliance with GDPR including data minimization, right to erasure, and transparent data processing.
WCAG 2.1 AA
The platform meets WCAG 2.1 AA accessibility standards, ensuring equal access for all voters regardless of ability.
Cloud Security
Hosted on Microsoft Azure with enterprise-grade security, DDoS protection, and high-availability architecture.
Trust the Math, Not the Promises
Every electobox election produces independently verifiable cryptographic proofs. Don't take our word for it — verify it yourself.
